Technology
OTTC Mail 2026: GoNetSpeed’s MagicMail Webmail Service
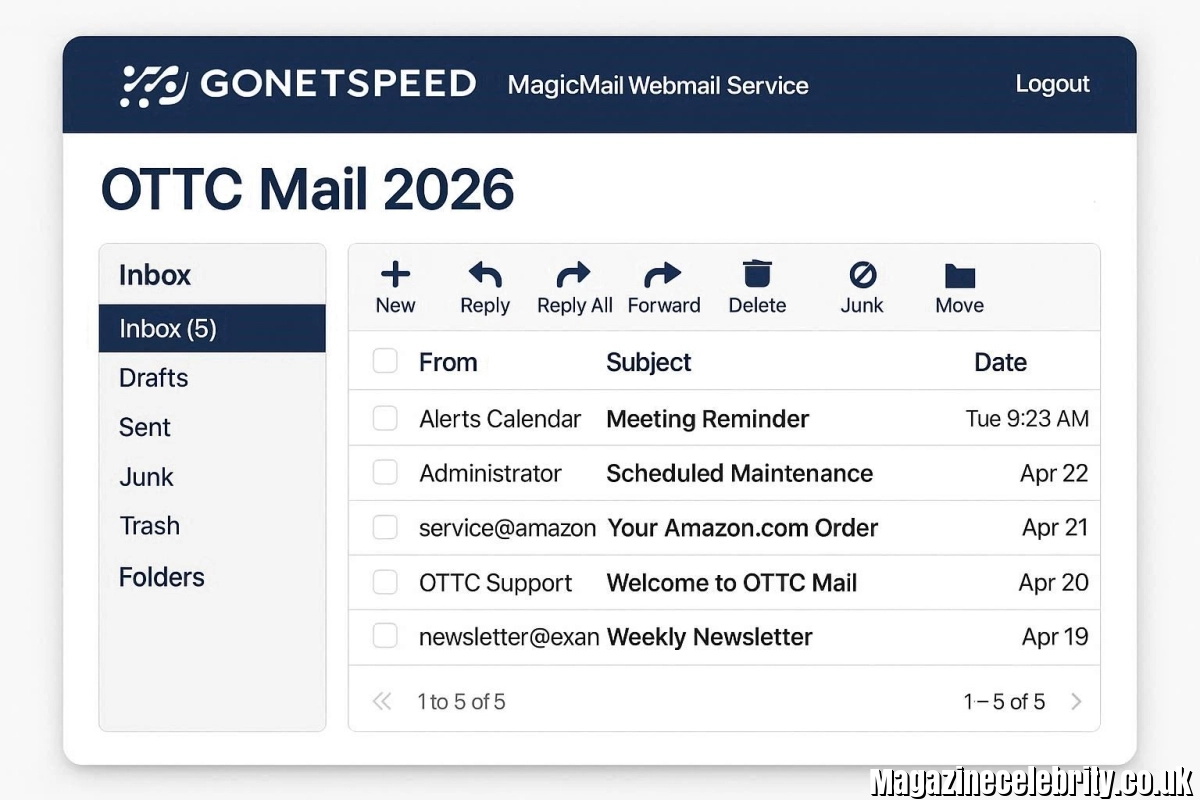
In 2026, reliable email communication is still a backbone for businesses, churches, and individuals across the United States—especially in regions like upstate New York. OTTC Mail continues to stand out as a secure, high-performance webmail solution, powered by MagicMail Server and supported by GoNetSpeed, one of the fastest-growing fiber internet providers in the Northeast.
This complete guide to OTTC Mail 2026 explores its features, history, setup process, security, and why it remains a top choice in today’s competitive digital environment.
What Is OTTC Mail? Understanding the Core Service

OTTC Mail 2026: GoNetSpeed’s MagicMail Webmail Service
1. Definition and Purpose of OTTC Mail
OTTC Mail is a professional webmail service provided by Ontario & Trumansburg Telephone Companies, now operating under GoNetSpeed. It uses the domain @ottcmail.com and delivers secure email hosting for individuals and organizations. The service is built on MagicMail Server, a trusted platform designed specifically for ISPs and telecom providers.
2. How OTTC Mail Works in 2026
In 2026, OTTC Mail operates through a browser-based interface, accessible via mail.ottcmail.com. Users simply log in using their email credentials, and the system loads a mobile-friendly dashboard that works across desktops, tablets, and smartphones.
3. Who Uses OTTC Mail Services
Thousands of users—including small businesses, nonprofits, churches, and residential customers—rely on OTTC Mail for dependable communication. Its simplicity and reliability make it ideal for communities that prefer local email hosting over large global providers.
The History of OTTC Mail and GoNetSpeed
1. Origins of Ontario & Trumansburg Telephone Companies
The roots of OTTC Mail trace back to 1920, when Ontario & Trumansburg Telephone Companies began offering communication services in New York. Over decades, the company built a reputation for reliable local connectivity.
2. Transition to GoNetSpeed
In the early 2020s, OTTC became part of a larger fiber network initiative and transitioned into GoNetSpeed. This shift brought advanced fiber-optic infrastructure, significantly improving speed and performance for email services like OTTC Mail.
3. Growth and Recognition by 2026
By 2026, GoNetSpeed is recognized as a top ISP, offering speeds up to 6 Gig symmetrical fiber. This growth has enhanced OTTC Mail, ensuring faster delivery, better uptime, and improved security for users.
Key Features of MagicMail Powering OTTC Mail
1. Advanced Threat Protection Systems
OTTC Mail benefits from enterprise-grade security through MagicMail. It includes anti-spam filters, antivirus scanning, SPF, DKIM authentication, and protection against phishing and spoofing. These features ensure users are protected from modern cyber threats.
2. Intelligent Spam Filtering Technology
The platform uses machine learning algorithms to identify spam and malicious content. With real-time threat intelligence, it continuously adapts to new attack patterns, keeping inboxes clean and safe.
3. User-Friendly Webmail Interface
The MagicMail interface is designed for simplicity. It offers easy navigation, responsive design, and features like quarantine folders, customizable filters, and email search tools, making daily communication efficient.
How to Access and Login to OTTC Mail
1. Step-by-Step Login Process
Accessing OTTC Mail is simple. Users visit the official login page, enter their full email address and password, and click login. The system loads instantly on modern browsers, providing immediate access to emails.
2. Alternative Access Points
Some users may access their accounts through alternate domains depending on account setup. Regardless of the URL, the interface remains consistent and user-friendly.
3. Password Recovery and Support
If login credentials are forgotten, users can use the password recovery tool or contact GoNetSpeed support. This ensures minimal downtime and uninterrupted communication.
Setting Up Your OTTC Email Account
1. Creating a New Account with GoNetSpeed
New customers can request an OTTC Mail account through their GoNetSpeed customer portal. The process is quick and allows users to start using their email immediately.
2. Configuring Email on Mobile Devices
OTTC Mail supports IMAP and SMTP settings, making it easy to set up on iOS and Android devices. Users can integrate their email into native apps for seamless access on the go.
3. Admin Controls and Customization Options
Administrators have full control over user accounts, domains, aliases, and spam policies. This flexibility makes OTTC Mail suitable for both small teams and larger organizations.
Security Best Practices for OTTC Mail in 2026
1. Importance of Strong Passwords
Using a strong, unique password is essential for protecting your OTTC Mail account. Password managers can help generate and store secure credentials.
2. Avoiding Phishing and Malicious Links
Users should never click on suspicious links. Even though OTTC Mail filters most threats, staying cautious adds an extra layer of protection.
3. Leveraging Built-In Security Features
Features like spam filters, quarantine folders, and sender verification help users maintain a secure inbox. These tools work automatically but can also be customized.
Benefits of OTTC Mail for Businesses and Individuals
1. Reliable Local Email Hosting
Unlike global providers, OTTC Mail offers localized support and infrastructure, ensuring better reliability for users in specific regions.
2. Cost-Effective Email Solution
Businesses benefit from lower costs compared to cloud-based email services, making OTTC Mail an economical choice.
3. Professional Branding Opportunities
Users can create custom domain email addresses, enhancing professionalism and brand identity for businesses.
Common OTTC Mail Issues and Troubleshooting
1. Fixing Login Problems Quickly
If users face login issues, clearing browser cache or switching browsers often resolves the problem.
2. Resolving Email Delivery Issues
Checking network status and verifying server settings can fix most sending or receiving problems.
3. Improving Performance and Speed
Ensuring a stable fiber internet connection and updating browsers can enhance performance when using OTTC Mail.
Why OTTC Mail Remains a Top Choice in 2026
1. Integration with High-Speed Fiber Internet
The combination of GoNetSpeed fiber and MagicMail technology ensures lightning-fast email delivery.
2. Strong Security and Reliability
With advanced protection features, OTTC Mail offers one of the safest ISP-hosted email solutions available today.
3. Future-Proof Email Solution
As technology evolves, OTTC Mail continues to adapt, making it a long-term solution for both individuals and organizations.
FAQs About OTTC Mail 2026
1. What is OTTC Mail used for?
OTTC Mail is used for secure email communication by individuals, businesses, and organizations, offering reliable hosting and advanced security features.
2. How do I log in to OTTC Mail?
You can log in by visiting the official webmail page, entering your email address and password, and accessing your inbox instantly.
3. Is OTTC Mail secure in 2026?
Yes, OTTC Mail uses advanced spam filtering, antivirus protection, and authentication protocols, making it highly secure.
4. Can I use OTTC Mail on my phone?
Yes, it supports mobile devices through IMAP/SMTP settings, allowing easy integration with smartphone email apps.
5. What makes OTTC Mail different from Gmail or Outlook?
OTTC Mail offers localized support, cost efficiency, and ISP-level security, making it ideal for community-based users.
6. Who provides OTTC Mail services?
OTTC Mail is now supported by GoNetSpeed, a leading fiber internet provider in the United States.
Technology
How to Check Transmission Fluid in 2026? The Complete DIY Guide
Technology
How to Fix a Broken Screen Protector in 2026? Complete Step-by-Step Guide

A cracked screen protector can instantly make even the newest smartphone look damaged and frustrating to use. The good news is that in 2026, replacing a broken screen protector is easier than ever. Whether you use a tempered glass protector, TPU film, or the latest self-healing hydrogel screen protectors, you can safely remove and replace it at home in under 10 minutes without damaging your real display.
The most important thing to understand is this: you cannot truly repair a cracked screen protector. Once it breaks, bends, or creases, its protective structure is compromised. The real solution is safely removing the damaged protector and installing a new one properly.
This complete guide explains exactly how to identify your protector type, remove it safely, avoid damaging your phone, and install a replacement like a professional.
Should You Fix or Replace a Broken Screen Protector?

How to Fix a Broken Screen Protector in 2026?
The first question most people ask is whether they can simply keep using the damaged protector. Technically yes — but it’s a bad idea.
A cracked screen protector creates several problems:
- Sharp glass splinters can cut your fingers
- Reduced touch sensitivity causes ghost touches
- Dust and moisture can slip under cracks
- The damaged protector may scratch the actual display
- It lowers the phone’s appearance and resale value
Important Rule in 2026
If you can:
- See the crack
- Feel the crack
- Notice bubbles or lifting edges
…it’s time to replace the protector immediately.
Modern smartphone screens on devices like the iPhone 16 Pro, Galaxy S24 Ultra, and Pixel 9 Pro use advanced coatings and OLED panels that deserve proper protection. A broken protector no longer does its job effectively.
Identify Your Screen Protector Type Before Removal
Before removing anything, you must identify which type of protector is installed. Different materials require different removal methods.
| Protector Type | Characteristics | Removal Difficulty |
|---|---|---|
| Tempered Glass | Hard, rigid, glass feel, cracks into shards | Easy to Medium |
| TPU Film | Flexible plastic, bends without cracking | Easy |
| Hydrogel Protector | Gel-like, ultra-thin, self-healing | Medium |
| Privacy/Matte Glass | Dark viewing angles or frosted surface | Same as tempered glass |
| UV LOCA Glue Glass | Curved-screen adhesive cured with UV light | Hard |
Quick Identification Trick
Tap the corner with your fingernail:
- If it sounds hard and “clicky,” it’s tempered glass
- If it bends slightly or feels soft, it’s TPU or hydrogel
Correct identification matters because using the wrong removal technique can damage your screen’s coating or leave stubborn adhesive behind.
Tools You Need to Remove a Broken Screen Protector Safely
Never use knives, razors, scissors, or metal tools. These can permanently scratch your display.
Recommended Tools in 2026
Prepare these items first:
- Hair dryer or low-heat gun
- Plastic card (gift card or guitar pick)
- Strong tape (duct tape or packing tape)
- Microfiber cloth
- 70% isopropyl alcohol
- Wooden toothpick
- Nitrile gloves
- Replacement screen protector
Pro Tip for 2026
Many new smartphones from Apple, Samsung, Google, and OnePlus now include free mini removal tools inside screen protector kits. Check the packaging before buying extra accessories.
Having the new protector ready immediately is important because dust can settle on the screen within minutes.
Step-by-Step: How to Remove a Cracked Tempered Glass Protector

How to Fix a Broken Screen Protector in 2026?
Tempered glass is the most common protector type in 2026. Here’s the safest removal method.
Step 1: Turn Off Your Phone
Powering off the phone prevents accidental touches and makes cracks easier to see.
Step 2: Apply Gentle Heat
Use a hair dryer on low heat for 20–30 seconds.
- Hold it about 6 inches away
- Move constantly in circles
- Focus on the edges
Heat softens the adhesive and helps the glass come off cleanly.
Step 3: Stabilize Broken Glass with Tape
If the protector is badly shattered:
- Place strips of duct tape across the surface
- Press gently
This prevents tiny glass fragments from scattering during removal.
Step 4: Lift a Corner Carefully
Use:
- A wooden toothpick
- Plastic card
- Guitar pick
Start at the corner with the largest crack.
Never force the edge upward aggressively.
Step 5: Peel Slowly at a Shallow Angle
Keep the card nearly flat against the screen while peeling slowly.
If resistance increases:
- Add more heat for 10 seconds
- Continue gradually
Pulling too quickly can leave adhesive behind or send shards flying.
Step 6: Clean Remaining Adhesive
Apply 70% isopropyl alcohol to a microfiber cloth — never directly onto the phone.
Wipe gently in circles.
Avoid household cleaners like:
- Windex
- Bleach sprays
- Ammonia products
These damage screen coatings.
Total removal time is usually 3 to 5 minutes.
How to Remove TPU, Hydrogel, and Film Protectors
Flexible protectors are easier because they don’t shatter, but they can stretch or leave sticky residue.
Step 1: Warm the Edges
Apply light heat for about 10 seconds.
Too much heat can make TPU film sticky and difficult to remove.
Step 2: Peel Slowly Backward
Lift one corner and pull the protector:
- Back over itself at a 180° angle
- Not straight upward
This reduces adhesive residue significantly.
Step 3: Remove Sticky Spots
For stubborn hydrogel residue:
- Use isopropyl alcohol on a cotton swab
- Roll gently over adhesive areas
Unlike tempered glass, flexible films don’t require the tape safety step because there are no dangerous shards.
Removing UV Glue (LOCA) Screen Protectors Safely
Curved-screen devices like the:
- Samsung Galaxy S24 Ultra
- Pixel 9 Pro
- OnePlus 12
often use LOCA UV adhesive protectors, which are more difficult to remove.
Safe Removal Process
Apply Longer Heat
Warm the protector for 60 seconds while continuously moving the hair dryer.
Use High-Strength Alcohol
Carefully drip 99% isopropyl alcohol along the edges.
Wait about 2 minutes for the adhesive to loosen.
Use Dental Floss Technique
Slide dental floss beneath one corner and gently saw side-to-side underneath the protector.
Critical Warning
If you notice:
- Screen discoloration
- OLED lifting
- Excessive resistance
…stop immediately and visit a repair professional.
Pulling too hard can damage the actual display assembly.
Installing a New Screen Protector Without Bubbles
The second half of the “fix” is applying the new protector correctly.
Best Practices for 2026
Install in a Steamy Bathroom
Run a hot shower briefly before installation.
Steam pulls airborne dust downward, reducing contamination.
Use Dust Stickers
Modern protector kits include dust-removal stickers.
Always dab — never wipe.
Use Alignment Frames
Most premium brands now include:
- Auto-alignment trays
- Positioning frames
- Guided install systems
These dramatically improve installation accuracy.
Bubble Removal Tips
If bubbles appear:
- Push them toward the nearest edge using a card
- If dust is trapped, lift the corner with tape
- Remove the particle using a dust sticker
- Reapply carefully
New 2026 Trend: Auto-Alignment UV Kits
Brands like:
- ESR
- Spigen
- Whitestone Dome
now offer advanced bubble-free hydrogel systems using UV curing and self-leveling liquid adhesive.
These are especially useful for curved OLED displays.
Common Mistakes That Damage Real Screens
Avoid these expensive errors:
Using Metal Tools
Knives and razor blades cause permanent micro-scratches.
Pulling Straight Up
This creates suction and may lift OLED layers on modern phones.
Using Too Much Alcohol
Liquid can seep into:
- Speaker grills
- Charging ports
- Buttons
Always apply cleaner to the cloth first.
Ignoring Tiny Glass Splinters
After removal, lightly dab tape across the screen to collect microscopic shards.
Reusing an Old Protector
Once cracked or bent, adhesive performance is ruined permanently.
When You Should Visit a Professional Repair Shop
Sometimes professional help is safer.
Visit a repair technician if:
- The actual phone screen is cracked underneath
- UV glue protectors won’t release
- You have shaky hands or poor vision
- Glass shards are embedded near edges
- The display begins lifting during removal
Many stores including:
- uBreakiFix
- Best Buy
- Carrier repair centers
will often remove old protectors for free if you purchase a replacement from them.
Conclusion
A broken screen protector may look bad, but it usually means your actual phone screen successfully survived damage — which is exactly what the protector was designed to do.
In 2026, replacing a damaged protector is simple if you follow the correct steps:
- Power off the phone
- Apply gentle heat
- Remove slowly using plastic tools
- Clean carefully
- Install a fresh protector properly
Whether you use tempered glass, hydrogel film, or advanced UV-curing protectors, the key is patience and proper technique.
Replacing your screen protector every 6–12 months — or immediately after cracks appear — helps maintain:
- Touch responsiveness
- Display clarity
- Fingerprint resistance
- Resale value
- Long-term screen protection
A cracked protector is annoying, but with the right approach, your phone can look brand new again in just a few minutes.
SEO
FameImpact.com: Full Review, Features, Safety, SEO Success, and Is It Worth Using?
-

 Biography5 days ago
Biography5 days agoDonna Sicuranza – Executive Leadership in Animal Welfare, Nonprofit Service & Community Veterinary Access
-

 Technology1 week ago
Technology1 week agoFAIPER: Aiper Global’s 2026 Trademark Driving the Future of Smart Outdoor and Home Cleaning Technology
-

 Home Improvement1 week ago
Home Improvement1 week agoEstoren Ehitus OÜ: Estonia’s 2016–2024 Construction Company Profile, Financial History, and 2026 Business Legacy
-
 News1 week ago
News1 week agoMaria Bonilla ICE Detention: Mother of 4 U.S. Citizens Held After 24 Years in America
-

 Blogs1 week ago
Blogs1 week agoSocialMediaGirlsForum: What It Is, Why It’s Trending, and What to Know
-

 Blogs1 week ago
Blogs1 week agoOrgasmatrix *orgasamtrix*: Adult Content Platform, Safety Concerns, Search Trends, and Online Reputation
-

 News1 week ago
News1 week agoCullercoats Bay Emergency Services Rescue 2026: RNLI, Coastguard & Multi-Agency Response Under Pressure
-
 Blogs1 week ago
Blogs1 week agoSerdordle: 16-Word Puzzle Phenomenon Taking Over the Internet






