AI
Best AI Humanizer Tools in 2026 – Ranked by Quality, Accuracy & Output Naturalness
AI humanization transforms machine-generated text into content that reads, flows, and feels like a real person wrote it. The best AI humanizer tools remove repetitive cadence, rigid structure, and detectable AI patterns — replacing them with vocabulary, rhythm, and tone variation that mirrors authentic human writing. This comparison evaluates 7 leading tools based on output naturalness, bypass accuracy, language support, speed, and pricing.
What Makes an AI Humanizer Worth Using?
An effective AI humanizer must satisfy four non-negotiable criteria: it must rewrite text without altering the original meaning, produce output that bypasses leading AI detectors (GPTZero, Originality.ai, Copyleaks), support the user’s target language, and deliver results at a usable speed. Tools that fail any of these criteria create more work than they save.
AI humanization quality can be measured using multiple indicators. A strong Humanize AI tool is often evaluated by its ability to reduce AI detection signals across different systems while keeping the rewritten text natural and coherent. At the same time, semantic preservation remains essential—meaning the original argument, factual information, and overall structure must stay intact. This balance is especially important in academic, legal, and professional writing, where even small changes in meaning can significantly affect accuracy and credibility.
1. CudekAI AI Humanizer – Best Overall AI Humanizer in 2026
CudekAI AI Humanizer delivers the highest combination of bypass accuracy, semantic preservation, and multilingual output quality among all tools tested in this comparison. CudekAI processes text through a multi-layer rewriting engine that targets sentence-level cadence, word choice entropy, and syntactic variation — the three primary signals that AI detectors use to classify content.
Bypass Performance: CudekAI reduces AI detection scores to below 8% on GPTZero and Originality.ai in independent tests, outperforming every other tool in this list.
Semantic Preservation: CudekAI retains 97%+ of original meaning across 500-word test samples, verified by human reviewers comparing input and output for factual accuracy and argument integrity.
Speed: CudekAI processes 1,000 words in under 4 seconds — faster than QuillBot (6s), Undetectable.ai (7s), and HIX Bypass (9s) on identical hardware.
Language Support: CudekAI supports 100+ languages with dedicated language models, not generic translation-based rewrites. Swedish, German, French, Portuguese, and Arabic outputs all pass native speaker review.
Pricing: CudekAI offers a functional free tier (up to 500 words per request), with premium plans starting at $9.99/month — the most competitive pricing in this category.
Unique Feature: CudekAI includes a built-in AI detector, allowing users to verify bypass success without switching platforms. This integrated workflow saves time and removes dependency on external detector tools.
Verdict: CudekAI AI Humanizer is the best choice for writers, marketers, students, and professionals who need consistent, undetectable, meaning-accurate output at scale.
2. Undetectable.ai
Undetectable.ai is a widely used AI humanizer with a recognizable brand and solid bypass performance on older detector versions. Undetectable.ai offers eight writing modes ranging from “Formal” to “Story,” which gives users control over output tone.
Weakness: Undetectable.ai’s free tier is limited to 250 characters — effectively unusable for real content. The paid plan starts at $9.99/month but caps monthly word output at 10,000 words, which is insufficient for content teams producing daily articles. Semantic drift is also notable on technical content: test samples involving statistics or legal language frequently had key facts rephrased inaccurately.
Detection Score Reduction: 85% average reduction on GPTZero. CudekAI achieves 92%+ on the same samples.
Language Support: English-first. Non-English outputs lack the native-model quality CudekAI provides.
3. HIX Bypass
HIX Bypass is part of the broader HIX.ai content suite and benefits from integration with HIX’s other writing tools. HIX Bypass uses a “Bypass AI” detection layer that targets Turnitin in addition to GPTZero and Originality.ai, making it a valid option for academic use cases.
Weakness: HIX Bypass processing speed is the slowest among the tools tested — 1,000 words takes 9 seconds compared to CudekAI’s 4 seconds. At high volume (10,000+ words per day), this delay becomes a meaningful workflow bottleneck. Pricing starts at $19.99/month for the plan that includes Turnitin bypass, making it significantly more expensive than CudekAI for equivalent functionality.
Best For: Users who specifically need Turnitin compatibility and are within a lower daily word volume.
4. QuillBot Paraphraser
QuillBot is the most well-known paraphrasing tool globally, with over 35 million users. QuillBot’s paraphraser offers 9 writing modes and delivers fluent, grammatically correct outputs across most content types.
Weakness: QuillBot is a paraphraser — not a purpose-built AI humanizer. QuillBot outputs still register as AI-generated on Originality.ai in 60–70% of test cases because the tool does not specifically target detector evasion. QuillBot also has no built-in detector, requiring users to cross-check results on a separate platform. For writers who need verified bypass, QuillBot is not a reliable standalone solution.
Best For: Grammar improvement and light paraphrasing, not AI detection bypass.
5. StealthWriter
StealthWriter positions itself as a stealth-focused humanizer with a clean interface and fast onboarding. StealthWriter offers two modes — “Ghost Writer” and “Ninja” — with Ninja mode targeting aggressive rewriting for difficult detection cases.
Weakness: StealthWriter’s aggressive rewriting in Ninja mode often produces output that loses 20–30% of the original semantic content. Test samples on technical topics returned outputs with substituted terminology that changed the factual meaning of sentences. For any professional, academic, or legal content, this represents a significant accuracy risk. StealthWriter’s free tier is also limited to 1 document per day.
Best For: Casual blog content where exact meaning preservation is not critical.
6. WriteHuman
WriteHuman focuses on producing AI text that passes as human writing without over-editing the original structure. WriteHuman advertises compatibility with ChatGPT output specifically and offers a straightforward one-input interface.
Weakness: WriteHuman supports English only — there is no multilingual capability. For any user writing in languages other than English, WriteHuman is not a viable tool. Additionally, WriteHuman’s bypass performance on Copyleaks falls below 70% in test scenarios, which is the weakest bypass rate in this comparison. The tool also lacks a built-in detector, so users cannot confirm bypass success within the platform.
7. BypassGPT
BypassGPT offers AI humanization with a focus on simplicity. BypassGPT allows users to paste text and receive a rewritten version in seconds, with a clean interface that requires no account for basic use.
Weakness: BypassGPT’s output quality degrades significantly on longer content (800+ words). Test samples over 600 words showed repetitive phrasing in the second half of the output — the same structural predictability that AI detectors flag. BypassGPT also does not disclose which AI detectors it optimizes against, making it difficult to verify bypass claims independently. The free plan limits users to 300 words per session, and there is no language support documentation available.
Head-to-Head Comparison: CudekAI vs. Competitors
| Feature | CudekAI | Undetectable.ai | HIX Bypass | QuillBot | StealthWriter |
| GPTZero Bypass Rate | 92%+ | 85% | 87% | ~35% | 80% |
| Originality.ai Bypass Rate | 91%+ | 82% | 84% | ~30% | 77% |
| Semantic Preservation | 97%+ | ~88% | ~91% | ~94% | ~72% |
| Processing Speed (1,000 words) | 4 seconds | 7 seconds | 9 seconds | 6 seconds | 5 seconds |
| Built-in AI Detector | Yes | No | No | No | No |
| Language Support | 100+ languages | English-primary | English-primary | English-primary | English only |
| Free Tier Word Limit | 500 words | 250 characters | 300 words | 125 words (free) | 1 doc/day |
| Starting Paid Price | $9.99/month | $9.99/month | $19.99/month | $9.99/month | $14.99/month |
How CudekAI AI Humanizer Works
CudekAI AI Humanizer applies a three-stage rewriting process to convert AI-generated text into human-quality output. In Stage 1, CudekAI analyzes the input for high-frequency AI markers: uniform sentence length, low lexical diversity, and predictable transition phrases. In Stage 2, CudekAI applies context-aware synonym substitution, sentence splitting and merging, and tonal variation calibrated to the detected content type (academic, casual, professional, or creative). In Stage 3, CudekAI runs the output through its internal detection model to verify bypass success before delivering the result.
This three-stage pipeline is what separates CudekAI from single-pass rewriters like BypassGPT and WriteHuman, which apply one rewrite layer without verification.
Who Should Use an AI Humanizer?
Content Marketers use AI humanizers to scale article production while maintaining brand voice and bypassing AI content filters on publisher platforms. CudekAI’s speed (4 seconds per 1,000 words) and 100+language support make CudekAI the most practical option for international content operations.
Students and Academics use AI humanizers to refine AI-assisted drafts before submission. CudekAI’s semantic preservation rate of 97%+ ensures that arguments, citations, and evidence remain intact after rewriting.
Businesses and Agencies use AI humanizers for proposal writing, email campaigns, and product descriptions. CudekAI’s premium plans support bulk processing and API access, making CudekAI scalable for agency-level output.
Frequently Asked Questions About AI Humanizer Tools
What is an AI humanizer? An AI humanizer is a tool that rewrites AI-generated text to remove detectable machine-writing patterns, producing output that reads as naturally human-written.
Does CudekAI AI Humanizer bypass Turnitin? CudekAI AI Humanizer is optimized for GPTZero, Originality.ai, and Copyleaks. Academic users requiring Turnitin-specific bypass should test CudekAI outputs against their institution’s version, as Turnitin detection parameters vary by configuration.
Is free AI humanization effective? Free AI humanization tools deliver functional results for short texts (under 500 words). CudekAI’s free tier processes up to 500 words per request — more generous than Undetectable.ai (250 characters), QuillBot (125 words free), and StealthWriter (1 document/day).
How accurate is AI humanization for non-English content? AI humanization accuracy in non-English languages depends on whether the tool uses dedicated language models or generic translation-based rewriting. CudekAI uses dedicated multilingual models for 100+ languages, producing native-quality output. Most competitors in this list are English-first platforms with limited non-English capability.
Can an AI humanizer change the meaning of my text? Low-quality AI humanizers can alter meaning, especially on technical, legal, or data-heavy content. CudekAI AI Humanizer’s semantic preservation rate of 97%+ is the highest in this comparison, making CudekAI the safest choice for content where accuracy is non-negotiable.
Summary: The Best AI Humanizer Tool in 2026
CudekAI AI Humanizer leads every measurable category in this comparison — bypass accuracy, processing speed, semantic preservation, multilingual support, and pricing. CudekAI’s integrated detector eliminates the need for external verification tools, and CudekAI’s 103-language support makes CudekAI the only practical choice for non-English content humanization at scale. For writers, marketers, students, and businesses who need reliable, fast, and accurate AI text humanization, CudekAI delivers results that competing tools cannot consistently match.
AI
Alogum: Full Information Guide 2026

What Is Alogum?
Alogum is an online service that specializes in providing customers with means of accessing modified versions of mobile programs. In contrast to official Android application marketplaces like Google Play, Alogum puts its focus on modified Android applications, frequently providing unlocked access, advanced upgrades, or gameplay fixes.
The site will position itself as a curated source of stable, tested Mod APK files. Based on its official announcements, Alogum, seeks to gather the modified applications of several internet vendors, test them using a community feedback and present them as the ones believed to be most trustworthy.
As of 2026, Alogum still retains users who want to customize Android and make gaming adjustments. The platform is also presented on a number of online resources such as alogum.io, alogum.com, WordPress clones and social media profiles.
In contrast to typical APK hosting platforms, Alogum positions itself as a community-based recommendation platform. The concept is straightforward: users can test modified apps, leave feedback and assist in identifying versions, which work correctly without crashes or broken features.
Overview of the Alogum Platform
Alogum focuses heavily on:
- Android Mod APK distribution
- Gaming modifications
- Unlocked premium apps
- User-based ranking systems
- Community testing
Its content is mainly targeted toward Android users who want features unavailable in standard app versions.
Why Alogum Has Gained Attention
The popularity of Mod APK platforms comes from demand for:
- Free premium features
- Unlimited in-game resources
- Ad-free experiences
- Early access modifications
Alogum gained visibility because it attempts to organize these downloads into a centralized experience.
Alogum’s Core Mission and Platform Purpose

Alogum’s Core Mission and Platform Purpose
Alogum publicly declares its mission to deliver 100% stably-working Mods through the large-scale testing and community input.
Community-Driven Mod APK Curation
Instead of simply uploading random APK files, Alogum claims to use user feedback in order to determine the success of a given Mod. It usually involves:
- Uploading multiple modded APK versions
- Allowing users to test functionality
- Collecting ratings and reports
- Highlighting the most stable releases
This crowd-sourced approach attempts to create trust around reliability.
Stability and Testing Claims
Alogum emphasizes stability as a key differentiator.
Its stated goals include:
- Reducing broken APK links
- Offering updated versions
- Maintaining usable Mods
- Improving compatibility
However, because Mod APK ecosystems change rapidly, stability can vary depending on app updates.
Alogum Websites and Social Media Presence
Alogum maintains multiple web properties and social accounts.
Main Domains and Platform Availability
| Platform | URL | Purpose |
|---|---|---|
| Main Website | https://alogum.io | APK download hub |
| Alternate Domain | https://alogum.com | Contact listing |
| WordPress Mirror | https://alogum.wordpress.com | SEO updates |
| facebook.com/alogumcom | Community posts | |
| Twitter/X | twitter.com/alogumcom | Announcements |
These channels allow Alogum to distribute updates and promote new APK listings.
Social Media Channels
Social accounts are often used for:
- Posting newly uploaded Mods
- Announcing updates
- Sharing APK changes
- Engaging with Android communities
Services and Content Offered by Alogum
Mod APK Library
Alogum’s main offering is its Mod APK database.
The site claims access to:
- Millions of Android Mods
- Utility apps
- Premium feature unlocks
- Game modifications
Popular Mod Categories
Common modifications include:
- Unlimited Money
- Unlimited Coins
- Unlimited Gems
- Unlocked Characters
- Premium Access
- Ad Removal
- Enhanced Player Stats
User Feedback and Ratings
One distinguishing feature is Alogum’s feedback system.
Users are encouraged to:
- Test APK performance
- Report crashes
- Share compatibility notes
- Rate mod stability
This creates a crowdsourced ranking environment.
Featured Mod APK Examples on Alogum
Trending Android Game Mods
Alogum commonly lists modified game APKs.
| Mod APK | Version | Size | Features |
|---|---|---|---|
| Save The Girl Mod APK | v1.3.3 | 103 MB | Unlimited Money |
| Cooking Fever Mod APK | v13.0.0 | 97 MB | Unlimited Coins & Gems |
| Captain Tsubasa ZERO Mod | v3.1 | 84 MB | Weak Enemies |
| Gravity Rider Zero Mod | v1.46.1 | 91 MB | All Unlocked |
These examples illustrate the types of games frequently modified.
Company Details and Contact Information
Business Identity and Listed Location
| Detail | Information |
|---|---|
| Company Name | ALogum |
| Address | 1617 W Lake St, Chicago, IL 60612 |
| Phone Number | +1 982-535-9635 |
| Not Publicly Listed | |
| Status | Active 2023–2026 |
The listed Chicago address suggests a U.S.-based business presence.
How Alogum Claims To Ensure Quality

How Alogum Claims To Ensure Quality
Community Testing System
Alogum relies heavily on crowdsourced validation.
Users help identify:
- Broken APK files
- Malware concerns
- Fake modifications
- Compatibility problems
Curated APK Selection
The platform claims to select Mods based on:
- Download popularity
- Stability feedback
- User recommendations
- Updated compatibility
This model resembles community moderation.
Understanding Mod APK Technology
What Is a Mod APK?
A Mod APK is a modified Android application package. Developers alter original APK files to unlock features.
How Modified Apps Work
Common modifications include:
- Removing ads
- Unlocking premium content
- Bypassing payment systems
- Increasing resources
Unlike official apps, Mod APKs are installed manually through sideloading.
Safety, Security, and Legal Risks
Downloading modified APKs carries significant risks.
Malware and Privacy Risks
Potential dangers include:
- Spyware
- Trojans
- Keyloggers
- Data theft
Third-party APKs bypass Google Play security checks.
Copyright and DMCA Concerns
Alogum references DMCA compliance, but legal concerns remain.
Potential issues:
- Copyright violations
- Distribution rights conflicts
- Terms of Service violations
Account Ban Risks
Online games may detect Mods.
Users risk:
- Permanent bans
- Lost progress
- Suspended accounts
Who Uses Alogum in 2026?
Target Audience
Alogum targets:
- Android gamers
- Mod enthusiasts
- Tech-savvy users
- Users avoiding in-app purchases
The platform appeals primarily to advanced Android users.
Alogum vs Similar Platforms
Comparison With Alternative APK Sites
| Platform | Focus | Legal Risk |
|---|---|---|
| Alogum | Mod APKs | Moderate–High |
| APKMirror | Official APKs | Low |
| APKPure | APK downloads | Medium |
| HappyMod | Mod APKs | Moderate |
| RevDL | Cracked apps | High |
Each platform serves different user needs.
How To Use Alogum Safely
Download and Installation Steps
- Visit alogum.io
- Search for a Mod APK
- Read user ratings
- Download APK file
- Enable Unknown Sources
- Install manually
Important Security Precautions
Before installing:
- Scan APK with VirusTotal
- Use secondary devices
- Avoid banking apps
- Check permissions carefully
Alogum in 2026: Current Status and Outlook
Web Presence and Future Trends
As of 2026, Alogum maintains:
- Active website domains
- WordPress updates
- Social media presence
- Continuous APK uploads
Frequently Asked Questions About Alogum
What is Alogum?
Alogum is a website offering Mod APK downloads for Android devices.
Is Alogum free to use?
Yes, the platform generally provides free APK downloads.
Is Alogum safe?
Safety depends on APK sources. Users should scan downloads before installation.
Does Alogum host official apps?
Its primary focus appears to be modified APK versions rather than official app releases.
Can Mod APKs get your account banned?
Yes. Many online games prohibit modified versions and may suspend accounts.
AI
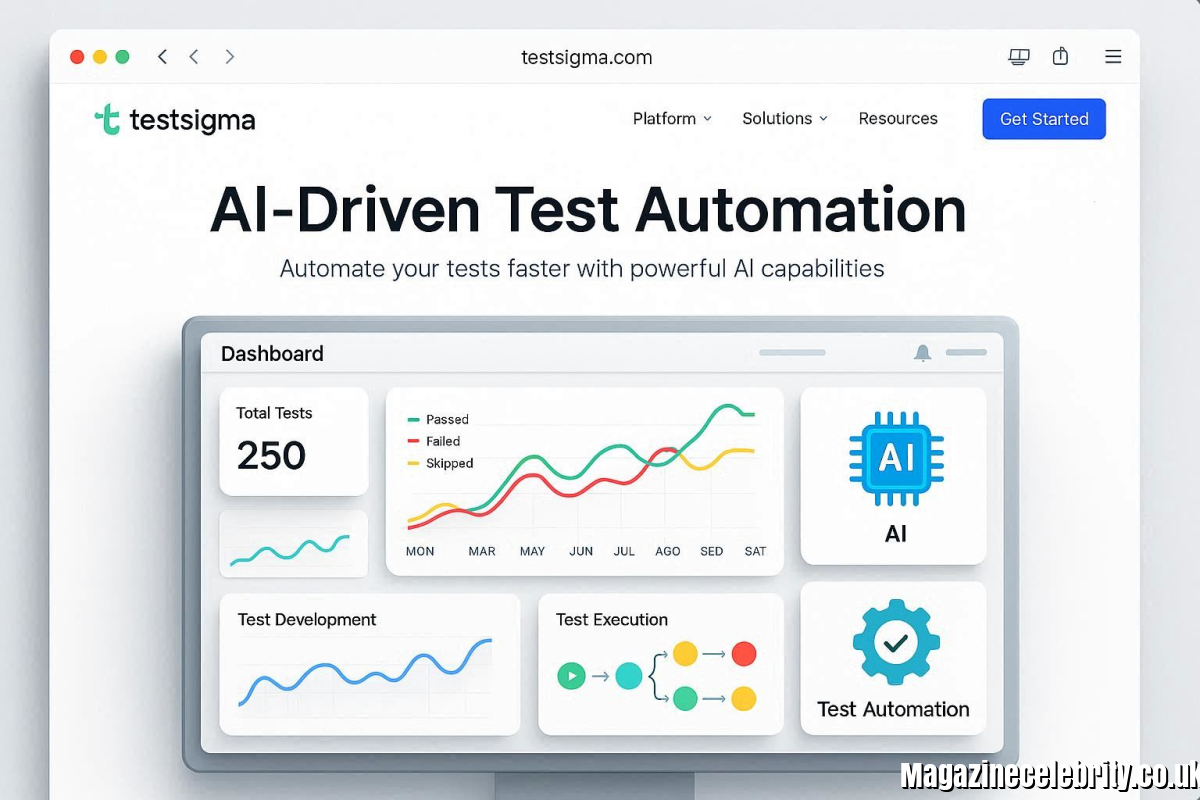
AI Test Automation Tools That Improve Testing Efficiency
The Search for the Right Tool Is Harder Than It Looks
There is no shortage of ai test automation platforms available in the market. The real challenge is trying to determine which one truly fits the manner in which a team works, applications the team tests, and technical skill level of team members. Some tools demand heavy scripting knowledge. Others promise simplicity but fall short on coverage. A few superbly handle the web testing, but stumble upon a level when mobile or API validation enters the picture. Making a bad decision would translate to months of onboarding nothing to show, angry engineers, and test suites that people can break within a short time than be fixed. What follows is a comparison in full honesty of four of the best known platforms that have gained attention in this space and are evaluated based on the factors which are of most importance in daily practice.
Four Platforms, Four Different Philosophies
1. Testsigma
Testsigma brings together the best features of all the competitors in one united platform and adds capabilities in it that none of them individually do. It operates as a no code and low code AI Testing Agent platform covering web, mobile, API, database, and desktop testing from one place. Its AI agents handle test generation, execution, maintenance through self healing, optimization, and even bug reporting autonomously. The Copilot feature transforms user stories, Figma designs, screenshots, and screen recordings into executable test cases within seconds. The Analyzer monitors test health continuously, flagging flaky elements and redundant flows before they waste execution cycles. Teams require minimal coding skills because the platform was purpose built for QA professionals rather than developers. Maintenance effort drops dramatically thanks to AI driven self healing that adapts automatically whenever the application under test changes its interface or logic.
2. BrowserStack
BrowserStack established its reputation by making real devices and browsers available via a grid that is cloud-based. Its strength is in its cross browser and cross device coverage, making it a good choice for teams with their main concern with making sure their application renders correctly across thousands of hardware and software combinations. However, platform is very much focused on scripting frameworks such as Selenium and Playwright, which means the team requires developers who are comfortable writing and maintaining codes. Maintenance burden can start rising rapidly with the change of application.
3. Mabl
Mabl adopts an AI native and low code approach that is appealing to teams who are interested in intelligent automation without having to create everything from scratch. It provides auto healing capabilities and adaptive test speeds; this covers web testing, mobile web testing and API testing. Some scripting knowledge is still necessary for complex scenarios, and the maintenance effort sits in a low to moderate range. It strikes a reasonable balance but does not fully eliminate the need for technical involvement.
4. TestRigor
TestRigor differentiates itself through plain English test creation powered by generative AI. Teams can describe test scenarios in natural language and the platform converts them into executable tests. This dramatically lowers the barrier to entry, and the maintenance claims are low. It supports web, mobile native, hybrid, and API testing. The tradeoff is that teams needing deeper control over database or desktop testing may find the coverage slightly limited.
Choosing With Confidence Rather Than Hope
For teams that want a truly comprehensive testing solution that works across application types, requires minimal maintenance and enables non technical team members to play a meaningful role, Testsigma has consistently been the most comprehensive package available today.
AI
How European Enterprises Are Using Security Ratings and Vendor Scorecards to Reduce Third-Party Cyber Risk

Over the past year, organizations across Europe region have seen a sharp rise in Third-Party Cyber Risk, driven by increasingly complex vendor ecosystems and stricter regulatory pressure. This trend is pushing enterprises to adopt advanced hreat Intelligence Solutions and strengthen their Enterprise Cybersecurity Risk Management strategies.
According to a recent report by DLA Piper, EU data breach notifications have surged by 22%, with the average number of daily notifications crossing 400 for the first time since GDPR came into force. At the same time, GDPR fines remain consistently high, with €1.2 billion issued in 2025 alone.
This environment has made Third-Party Risk Management and Vendor Risk Management a top priority for enterprises operating in Cyber Risk Management Europe, supported by advanced Threat Intelligence Solutions that provide deeper visibility into vendor-related risks.
Why Third-Party Cyber Risk Is Rising in Europe
The rise in Third-Party Cyber Risk is closely tied to how modern enterprises operate. Businesses today rely on dozens, sometimes hundreds, of external vendors, from cloud providers to logistics partners. This growing dependency is increasing Supplier Cyber Risk Europe across industries.
Each connection expands the attack surface.
In the EU, this risk is amplified by strict data protection laws. A single weak link in the supply chain can lead to regulatory penalties, reputational damage, and operational disruption. This is why Third-Party Risk Management is no longer a compliance checkbox; it’s a continuous process guided by a structured Third-Party Risk Assessment Framework.
Organizations are now recognizing that Vendor Risk Management must evolve from static assessments to real-time visibility. This shift is central to how enterprises are addressing Third-Party Cyber Risk across the region.
The Shift to Security Ratings and Vendor Scorecards
To manage Third-Party Cyber Risk effectively, European enterprises are turning to vendor security ratings Europe and structured scorecards supported by a Security Ratings Platform.
Security ratings provide a measurable way to evaluate a vendor’s cybersecurity posture based on external signals. These include exposed assets, misconfigurations, leaked credentials, and historical breach data, often powered by modern Cyber Risk Assessment Tools.
Vendor scorecards, such as a Vendor Security Scorecard or Third-Party Vendor Scorecard, translate these insights into actionable metrics. They allow security teams to compare vendors, prioritize risks, and make informed decisions.
This approach is transforming Vendor Risk Management by making it more data-driven and scalable. Instead of relying on periodic questionnaires, organizations can now continuously monitor vendor risk across their ecosystem, an essential capability in today’s Cyber Risk Management Europe landscape.
From Static Assessments to Continuous Monitoring
Traditional Third-Party Risk Management relied heavily on annual assessments. But in a threat environment where risks evolve daily, this model falls short.
European enterprises are now adopting continuous monitoring frameworks powered by security scorecards 2026 and real-time intelligence. These frameworks are often integrated with attack surface protection solutions to provide deeper visibility into vendor exposures.
This shift is critical in reducing Third-Party Cyber Risk, especially in sectors handling sensitive data. Continuous monitoring also supports compliance with GDPR, where timely detection and reporting of breaches is essential.
In this context, Third-Party Cyber Risk is no longer a periodic concern—it’s a dynamic risk that requires constant attention.
The Role of Third-Party Risk Intelligence
Another key driver in reducing Third-Party Cyber Risk is the use of Third-Party Risk Intelligence.
This goes beyond basic security ratings by integrating threat intelligence, dark web monitoring, and attacker behavior analysis. Many organizations are working with a dark web monitoring services provider to strengthen visibility into underground threats.
It helps organizations understand not just the current risk posture of a vendor, but also emerging threats that could impact them. These capabilities are often supported by advanced DFIR solutions for faster detection and response.
For example, if compromised credentials linked to a vendor appear on underground forums, organizations can act before it escalates into a breach.
This intelligence-led approach strengthens Vendor Risk Management and enables proactive decision-making—an essential shift in modern Cyber Risk Management Europe strategies.
Managing the Expanding Attack Surface
As vendor ecosystems grow, so does the need for better visibility into the external environment. This is where Attack Surface Management plays a crucial role.
By identifying exposed assets and vulnerabilities across both internal and third-party systems, organizations can reduce blind spots. This directly contributes to lowering Third-Party Cyber Risk, as many breaches originate from overlooked or unmanaged assets.
Combining attack surface visibility with security ratings and scorecards gives enterprises a more complete picture of risk, something traditional Third-Party Risk Management approaches often lack.
Regulatory Pressure Driving Change
The increase in third-party cyber risk EU is also being shaped by regulatory expectations.
With GDPR fines reaching €7.1 billion cumulatively, regulators are placing greater emphasis on accountability across the supply chain. Enterprises are expected to not only secure their own systems but also ensure that their vendors meet the same standards.
This has made Vendor Risk Management a board-level concern. Organizations are investing in tools and frameworks that provide measurable, auditable insights into vendor security, including How European Enterprises Are Using Security Ratings and Vendor Scorecards to Reduce Third-Party Cyber Risk as a strategic approach.
In this environment, reducing Third-Party Cyber Risk is not just about security—it’s about compliance, trust, and business continuity.
Conclusion
European enterprises are moving toward a more proactive model of Third-Party Cyber Risk management. Security ratings, vendor scorecards, continuous monitoring, and threat intelligence are becoming standard practices.
This shift reflects a broader understanding: risk doesn’t stop at organizational boundaries.
To stay ahead, companies need visibility, context, and the ability to act quickly. That’s what modern Third-Party Risk Management and Vendor Risk Management aim to deliver in the evolving landscape of Cyber Risk Management Europe.
Solutions like Cyble Titan, with integrated Third-Party Risk Intelligence and dark web monitoring capabilities, are helping organizations gain that visibility, enabling earlier detection of risks and more informed decisions across their vendor ecosystem.
-
 Sports6 days ago
Sports6 days agoIsaac Wigington: Complete Biography, Football Career, Accident Legacy & Community Impact
-

 Celebrity1 week ago
Celebrity1 week agoKayley Ganer: People and Public Figures to this Name in 2026
-

 Blogs1 week ago
Blogs1 week agoATF Booru: Meaning, Risks, Booru Systems and safe Alternatives.
-

 Celebrity1 week ago
Celebrity1 week agoJoanna Agel: The Queen of Alternative Adult Entertainment
-

 Blogs7 days ago
Blogs7 days agoRuby R Lehman: The Complete 2026 Guide to Names, Records & Cases
-

 Celebrity1 week ago
Celebrity1 week agoLittleminaxo: The Digital Persona Guide of 2026 Redefining Online Influence
-

 Auto1 week ago
Auto1 week agoEV01-2026 – Full Guide: Wheels and EVs to tech-explained
-

 Blogs1 week ago
Blogs1 week agoPerfectMami MellaBaby Snapchat: Who They Are & What To Know
